Once I needed to forward a port to a VPN server that had a gray IP address and was behind NAT.
Continue reading “Port forwarding in iptables on NAT server”Category Archives: Networks
How to change gateway in Linux
Once I needed to change the default gateway on different servers without restarting the network service or rebooting the server, I will give examples of how I did this.
Continue reading “How to change gateway in Linux”How to add a blackhole route in Netplan
I will give an example of setting up blackhole routes in Netplan.
Continue reading “How to add a blackhole route in Netplan”“Pings drop out” on GPON ONU and defective power supplies
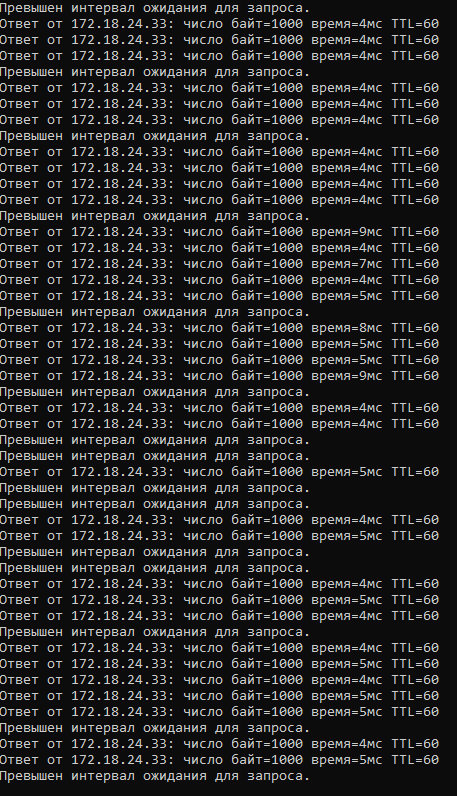
One day, several technical specialists who connect the Internet to users began to complain that there was no speed and ping requests “dropped out”.
iPerf Mulicast
I will show an example of running iPerf to test network bandwidth using UDP Multicast.
Continue reading “iPerf Mulicast”How to set up iBGP in Bird
For example, I will configure the internal BGP protocol in Bird, in my case iBGP was needed in order to transfer user routes from several access servers to a NAT server. As access servers, I configured Accel-ppp (ipoe) and JuniperMX, they all worked simultaneously and balanced users by making an artificial DHCPOFFER delay.
Continue reading “How to set up iBGP in Bird”Configuring Juniper MX and ABillS
For example, I will configure the Juniper MX204 to work with the ABillS billing system.
Continue reading “Configuring Juniper MX and ABillS”Configuring OSPF in BIRD
In this article, I will give an example of configuring OSPF in BIRD.
Continue reading “Configuring OSPF in BIRD”Renaming Network Interfaces in Linux
Once, after updating the i40e driver for Intel network adapters, I noticed that the names of the network interfaces had changed, and after rebooting the operating system, the names also periodically changed.
Continue reading “Renaming Network Interfaces in Linux”Installing and configuring BIRD (BGP)
For example, I will install BIRD on Ubuntu Server 20.04 and show an example of configuring BGP.
